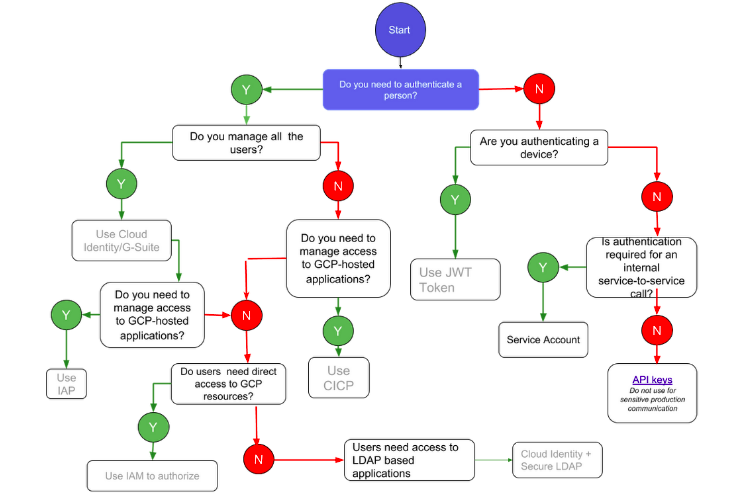
GCP offers a no. of solutions for Authentication and Identity management. Below are a few examples for the same.
- Cloud Identity: It is a Identity as a service (IDaas) solution that centrally manages users and groups. You can use it to identify the identities of google and other identity providers. It is also considered as a unified identity, app, access, and endpoint management platform which helps IT and security teams to protect company data, maximize end-user efficiency, and transition to a digital workspace. You can also gain more control for the account used in your organization. By using Cloud identity you can also create cloud identity accounts for each user and groups. You can also then use IAM to manage and control access of Google Cloud resources for all cloud identity accounts.
- Secure LDAP: It provides a simple and secure way to connect the Secure LDAP with the LDAP based application and services to Cloud identity. For authentication, authorization, and directory lookups you can also use the cloud directory as a cloud based LDAP. The IT infrastructure and LDAP based apps that you connect to the Secure LDAP service can be either on-premise or in iaas platforms. It is also used to reduce the traditional directory server footprint. You can manage the Secure LDAP service from Google admin console.
- Cloud Identity for Customers and Partners: It is also known as customer identity and access management platform. CICP is used to add Google-grade identity management functions in your app. It also provides token brokerage service which will help to manage end users credentials. It is used to provide an end to end authentication system for all the third party users who access your apps and services.

- Cloud Identity-Aware Proxy: It is used to access any cloud based application by verifying the user identity and context of the request. Cloud IAP determines if the user can access the app or not. If any user tries to access any app which is secured by Cloud IAP then the Cloud IAP performs authentication and authorization tests. If you are using any app using cloud IAP then fine-grained access controls are implemented by the cloud IAP service. It also helps employees to work from any untrusted networks without using VPN. Context aware access is used to verify if the user is trusted or not. It will only allow you to access the app if the Cloud IAP’s machine-learning detects no abnormal behaviour. The endpoint verification is also used to verify the access of any user.
There are few more solutions for Authentication and Identity management. You can refer to the chart below to know more about this.