Terraform created by Hashicorp is a configuration orchestration tool as well as an open source software tool. Hashicorp’s terraform has a market share of 4.82 percent in the configuration management market. Top industries that use Hashicorp terraform for configuration management are devops, cloud & kubernetes. Around the world in 2021, over 591 companies have started using hashicorp terraform as configuration management tool. By using Terraform, we can provision the resources in Google Cloud Platform (GCP).
Let’s take a look at the advantages & disadvantages of Terraform:
Advantages/benefits of Terraform
1) Improve multi-cloud infrastructure deployment
2) Automated infrastructure management
3) Uniform Syntax for Infrastructure as Code
4) Reduced development costs
5) Reduced time to provision
6) Open Source
7) Support of various cloud solutions
8) Highly expandable
9) Storage and import function for existing architectures
10) Ability to generate dependency graphs
Disadvantages of Terraform
1) Demanding entry
2) No automatic rollback function for incorrect changes to resources
3) Collaboration and security features available only in expensive enterprise plans
Let’s know about the fundamentals of Terraform and how to apply them to GCP.
Terraform uses a service account to create and manage resources in the Google Cloud project.
Explore some commonly used Terraform commands:
1) terraform init – To download the provider needed to communicate with the REST API of the GCP & to validate it
2) terraform plan – Provides us the number of view of the changes that will be applied to the GCP Cloud / Shows a preview of what will be created
3) terraform apply – Applying the changes by calling Google Cloud APIs to set up the instances
4) terraform destroy – Thankfully, Terraform will let you remove all the resources defined in the configuration file. At the end, deleting the created resources.
Why one must go for terraform & what actually it is?

Why one must use terraform?
Reasons why one should consider terraform are:
Terraform lets you define infrastructure in configuration code & will enable you to rebuild & track changes to infrastructure with ease. So, terraform provides a high level description of infrastructure which means its infrastructure descriptive.
Second, it has a lively community & is open source. Many people are already using this tool & it’s easier to find people who know how to use it like plugins, extensions, professional support, etc. This also means terraform is evolving a much faster rate. They do releases very often.
So, third is like speedy operations. Terraforms speed & operations are like exceptional. One cool thing about terraform is its planned command lets you see what changes you are about to apply before you apply them. Code reuse features & terraform tends to make most changes faster and similar tools like Cloud Formation. Terraform matches correctly with what you want to do the API alliance with the way you think about infrastructure.
Also, like terraform is the only sophisticated tool that is completely platform agnostic as well as supports other services while there are a few alternatives but they are focused on a single cloud provider. There’s a declarative code. So, terraform enables you to implement all kinds of coding principles like having your code in source control, the ability to write automated tests, etc.
What terraform actually is?
Terraform is a configuration orchestration tool designed to provision the servers themselves. It refers to arrangement & coordination of automated tasks resulting in a consolidated process of workflow. So, it is also like open source tool means open source software tool created by Hashicorp. It’s created to manage present as well as popular service along with the custom in-house solutions.
Terraform lets you provision google cloud resources with declarative configuration files resources such as virtual machines, containers, storage & networking. Terraforms infrastructure is a code that is ISC approach, supports devops best practices for change management which lets you manage terraform configuration files in source control to maintain an ideal provisioning state for testing & production environments. Terraform manages external resources with providers. External resources like public cloud infrastructure, private cloud infrastructure, network appliances, software as a service & platform as a service.
Tools for using Terraform with Google Cloud
Let’s briefly understand the variety of tools you can use to optimize your Terraform experience:
1) Cloud Foundation Toolkit
First let’s explore the Cloud Foundation Toolkit which provides a series of reference modules for terraform. The modules are documented in the Terraform registry & open sourced on github. So, these are some of the features of Cloud Foundation Toolkit.
- First is ready-made templates. It provides a series of reference templates for deployment manager & terraform which reflect Google Cloud best practices. These templates can be used off the shelf to quickly build a repeatable enterprise radio foundation in Google Cloud. With infrastructure as a code you can easily update the foundation as your needs change.
- Second, you can treat your infrastructure like software. So, through the open source templates you can automate repeatable tasks & provision entire environments in a consistent fashion. Plus, your teams can collaborate on the infrastructure by participating in code reviews & suggesting source code changes.
- Third, it’s like built for enterprise. The Cloud Foundation Toolkit is designed spatially to meet the compliance & security needs of enterprises by creating a foundational environment. Using these templates you can be confident that best practices are implemented out of the box including key security & governance controls. Also, you can maintain consistency easily by adopting the toolkit you can be confident that different teams are deploying their applications & environments using a consistent set of tools & patterns. This reduces the potential for misconfigurations & inconsistencies while along easier collaboration across different teams. Also, you can choose your adoption strategy. You can choose which patterns make sense for your organization & add new ones as your environment evolves. The open source templates can easily be formed & modified to suit your organization’s needs.
- Lastly, you can save time & resources with pre-built templates. With the Cloud Foundation Toolkit, you don’t need to spend time developing your own templates & patterns for Google Cloud. Instead, you can build and open source templates & focus only on the customizations which are required to your company & workloads. Developers can like move faster & migrations are less time consuming because of it.
2) Terraform Validator
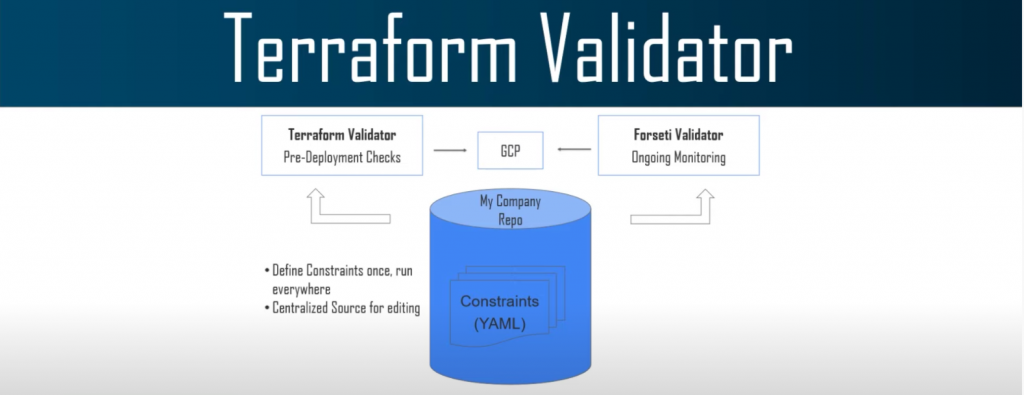
Terraform validator can be leveraged to enforce policies on terraform configurations for Google Cloud. It’s a tool used for validating compliance with organizational policies prior to applying terraform plan. It can be used either as a standalone tool or in conjugation with other policy enforcement tooling. Note that, using terraform validator does not require an active installation. Terraform Validator is a self-contained binary. So, Config validator helps cloud admins put guard rails in place to protect against mis-configurations in Google Cloud Platform environments. This allows developers to move quickly & give security & governance teams the ability to enforce security at scale.
How does the terraform validator works?
So, cloud admins write security & governance constraints as yml files once & store them within their company’s dedicated git repo as a central source of truth. Then the facility ingests constraints & uses them as a new scanner to monitor for violations. It reads the same constraints to check for violations before provisioning in order to help prevent misconfigurations from happening. That’s how the whole process of terraform validator works.
3) Terraformer
The next tool we have is Terraformer. We can import existing Google Cloud resources into Terraform with Terraformer. It is a command line interface tool that generates tf or json & tier state files. Terraform already has existing resources in your environment performing the reverse of what terraform is designed to do. This tool can mainly be thought of as infrastructure to code.
4) Cloud Shell
Next & the last tool is Cloud Shell. Using Cloud Shell you can manage your infrastructure & develop your applications from any browser. Cloud Shell is an online development & operations environment accessible anywhere with your browser. You can also develop, build, debug & deploy your cloud-based apps using the online cloud share editor. So, some of the features of Cloud Shell are like full power access from anywhere. You can manage your Google Cloud resources with the flexibility of a linux shell. Cloud Shell provides command line access to a virtual machine instance in a terminal window. Then, it has a developer ready environment. So, you can develop your apps directly from your browser with the Cloud Shell editor streamlined to increase your productivity with features such as go, java, node.js, python & C language support.
An integrated debugger source control refactoring & a customizable interface. Run your app on the Cloud Shell virtual machine or in the mini cube kubernetes emulator. Preview it directly in your browser then commit changes back to your wrapper from your grid clients.
Then, the next feature is like your favorite tools pre-installed & up-to-date. So, many of your favorite command line tools from bash & sh to max & vim are already pre-installed & kept up to date with Cloud Shell. Admin & development tools such as command line tool, mysql, kubernetes, docker, mini cube are configured & ready to use. No more hunting around for how to install the latest version & all its dependencies. Just connect to Cloud Shell & go.
Conclusion

Hashicorp’s Terraform is cool. It’s idempotent. We can automate the deployment with Terraform. I wonder how Terraform compares to its seemingly main competitor – Deployment Manager. For automating your infrastructure, Terraform truly is an awesome tool. It’s cross-platform nature and easy integration with Ansible mean that automation is only going to get easier for DevOps business. So far there are few interesting Terraform features to explore.
Now go forth and Automate All The Things!
You will make your life a lot easier, if you implement these principles and methodologies in your application lifecycle management. I hope you all have found this blog post on “Terraform in GCP” helpful.